Security risks and innovative cyber criminals are nothing new, however, when we work from home, these risks increase expeditiously. The only way we can combat security breaches is by adding extra measures of which multi-factor authentication (MFA) is one.
Information Technology is currently rolling out MFA. Most staff and students have already registered. If you haven’t, we ask that you urgently do so as all users will require to use MFA to access some services. The first services that will need MFA authentication are the Microsoft365 applications. These include Outlook and Teams.
A guide on how to register is available at the bottom of this article and everything you need to know about MFA at Stellenbosch University can be found on our service catalogue.
WHAT IS MULTI-FACTOR AUTHENTICATION (MFA)?
Multi-factor authentication (MFA) seeks to decrease the likelihood that others can access your data.
Specifically, it enhances the security of your UserID by using your phone, tablet or other device to verify your identity when you attempt to access Stellenbosch University’s network and resources.
It takes two items to access and update your information: “something you know” (e.g. your password) and “something you have” (e.g. your phone). For example, when you visit an ATM, one authentication factor is the ATM card you use to start the transaction – that’s the “something you have.” Next, you enter a PIN, which is the “something you know.” Without both these factors, your authentication will fail.
WHY DO I NEED TO USE MFA?
Passwords are becoming increasingly easy to compromise. They can be stolen, guessed and hacked and new technology and hacking techniques combined with the limited pool of passwords most people use for multiple accounts means information online is increasingly vulnerable. You might not even know who else has your password and is accessing your accounts.
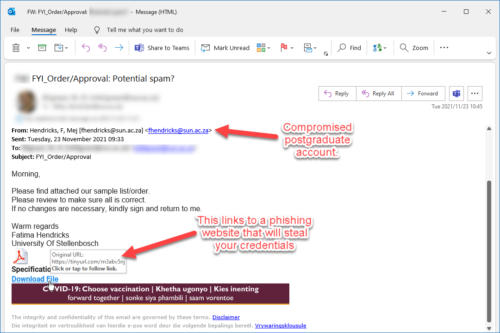
In addition, experience has shown that people are not as good at recognising malicious email as you might think. Every day, members of the Stellenbosch University community fall prey to cyber scams. Imagine you work on the University’s financial system. You click on what seems to be a legitimate email, typing in your username and password. A criminal now has your login details and can access everything you can access – including, potentially, bank details. In this way HR systems can be accessed and hacked preventing salaries from being paid paid out, etc. The possibilities are endless if someone has usernames and passwords.
We must take steps to ensure that we are more than just a single click away from having our pay check stolen or becoming a victim of identity theft.
Multi-Factor Authentication adds a second layer of security to your account to ensure that your account stays safe, even if someone else knows your password. This second factor of authentication is separate and independent from the UserID and password step — MFA never uses or even sees your password.
HOW DO I REGISTER FOR MFA?
You can register for MFA by following the steps in this guide.
Read more on MFA:
Back to basics: Multi-factor authentication (MFA)
What is Multi-factor authentication? And why is it important?
Video on MFA by tech expert Tom Scott.



 Microsoft recently sent out a notification that some versions of Office 2013 and Office 2016 may experience connectivity issues due to the retirement of support for these versions. It is therefore imperative that all users who still use Office 2013 and Office 2016 immediately upgrade their Office software to Office 365.
Microsoft recently sent out a notification that some versions of Office 2013 and Office 2016 may experience connectivity issues due to the retirement of support for these versions. It is therefore imperative that all users who still use Office 2013 and Office 2016 immediately upgrade their Office software to Office 365.  Part of living in a connected world is understanding that our private information is more vulnerable. ID theft and data breaches are no longer isolated incidents, they happen every single day.
Part of living in a connected world is understanding that our private information is more vulnerable. ID theft and data breaches are no longer isolated incidents, they happen every single day. The US government’s Cybersecurity and Infrastructure Security Agency has made a collection of tip sheets available for use. These downloadable PDF documents contain all the information you need to protect yourself from cyber security risks in a convenient, compact format.
The US government’s Cybersecurity and Infrastructure Security Agency has made a collection of tip sheets available for use. These downloadable PDF documents contain all the information you need to protect yourself from cyber security risks in a convenient, compact format.