[:en]
Due to the current working-from-home situation we are likely to spend more time either in a teams meeting or on a Zoom call. Those working from home might have experienced a sharp increase in the number of virtual meeting invites since lock down started last year.
We are either bouncing from one meeting to the other or struggling to schedule meetings, trying to establish who’s available and who’s not. This might be a short-term overreaction to the lack of other communication channels and social contact, but it could get in the way of productivity and efficiency.
Productive meetings are ones where you need to share expertise and the topics discussed require synchronous collaboration – where people need to be live at the same time, if not the same place. It is also helpful if you are dealing with conflict or need to build closer relationships.
On the other hand, if there’s no clear outcome, the topics are irrelevant, the outcome could be delivered without a meeting or you have no active role except to listen, then you may want to decline the meeting invitation. Typically, if we look at meeting content 40% of meetings are not necessary at all.
If you accept meeting invitations by default, particularly those without an agenda, you are saying that what the other person wants to talk about is a better use of your time than your own work.
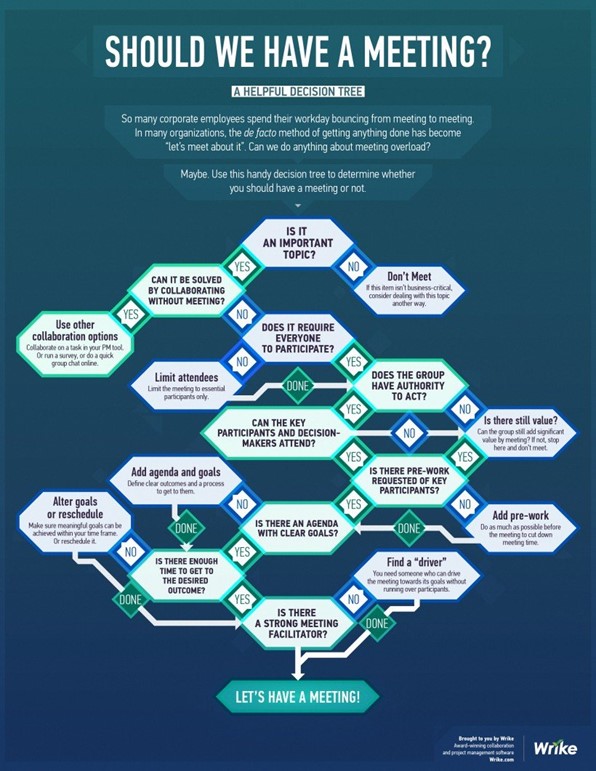
Declining meetings can be a challenge to existing meeting agendas and fixed ways of working, but discuss the necessity of a meeting with your meeting leader. This could open up a discussion in your team about which topics you need to discuss and which are not important. Below is an infographic decision tree which might help you or your colleagues reconsider scheduling a meeting.
Take this opportunity to improve your meetings, save yourself time and improve on working towards a productive environment.
SOURCE: https://www.wrike.com/blog/meeting-infographic-decision-tree/
[ARTICLE BY MANDY WANZA]
[:af]
Gegewe die huidige werk-van-die-huis situasie is ons meer geneig om ons werksure te spandeer in `n teams-vergadering of op `n Zoom-oproep. Diegene wat van die huis af werk sal moontlik `n skerp toename opgemerk in die hoeveelheid virtuele vergaderings waarheen hulle uitgenooi word sedert grendeltyd afgeskop het verlede jaar.
Die meeste van ons spring van een vergadering na die ander of probeer vergaderings skeduleer wat almal se reeds vol skedules pas. Hierdie optrede mag `n korttermyn oorreaksie wees weens die gebrek aan ander kommunikasievorme en sosiale kontak, maar dit kan produktiwiteit en effektiwitit beinvloed.
`n Produktiewe vergadering is een waar dit kennis gedeel moet word en die bespreekte onderwerpe gemeenskaplike samewerking benodig – waar mense terselfdertyd aanlyn moet wees, verkieslik op dieselfde plek. Dit is ook nuttig as konflik hanteer moet word of beter verhoudings gebou moet word.
As `n vergadering egter geen duidelike uitset toon, die onderwerpe irrelevant is, die uitkoms bepaal kon word sonder `n vergadering of jy slegs teenwoordig is om te luister en nie insette te gee nie, kan jy dit oorweeg om die uitnodiging van die hand te wys. Oor die algemeen is 40% van vergaderings nie werklik nodig nie.
Indien jy by verstek bloot uitnodigings na vergaderings aanvaar, veral dié sonder `n agenda, bevestig jy dat dit waaroor die ander persoon wil praat `n beter benutting is van jou tyd as jou eie werk.
Om vergaderinguitnodigings van die hand te wys kan `n uitdaging wees, veral met reeds geskeduleerde vergaderings. Dit kan egter die geleentheid bied om `n gesprek te begin met jou span oor watter onderwerpe nodig is om te bespreek en watter minder belangrik is. Onder is `n grafiese voorstelling wat jou en jou kollegas kan help om te besluit of `n vergadering nodig is.
Gebruik hierdie geleentheid om jou vergaderings to verbeter, tyd te spaar en `n verbeterde, produktiewe werksongewing te skep.
BRON: https://www.wrike.com/blog/meeting-infographic-decision-tree/
[ARTIKEL DEUR MANDY WANZA]
[:]
 Part of living in a connected world is understanding that our private information is more vulnerable. ID theft and data breaches are no longer isolated incidents, they happen every single day.
Part of living in a connected world is understanding that our private information is more vulnerable. ID theft and data breaches are no longer isolated incidents, they happen every single day.

 The US government’s Cybersecurity and Infrastructure Security Agency has made a collection of tip sheets available for use. These downloadable PDF documents contain all the information you need to protect yourself from cyber security risks in a convenient, compact format.
The US government’s Cybersecurity and Infrastructure Security Agency has made a collection of tip sheets available for use. These downloadable PDF documents contain all the information you need to protect yourself from cyber security risks in a convenient, compact format.  Before
Before