[:en]
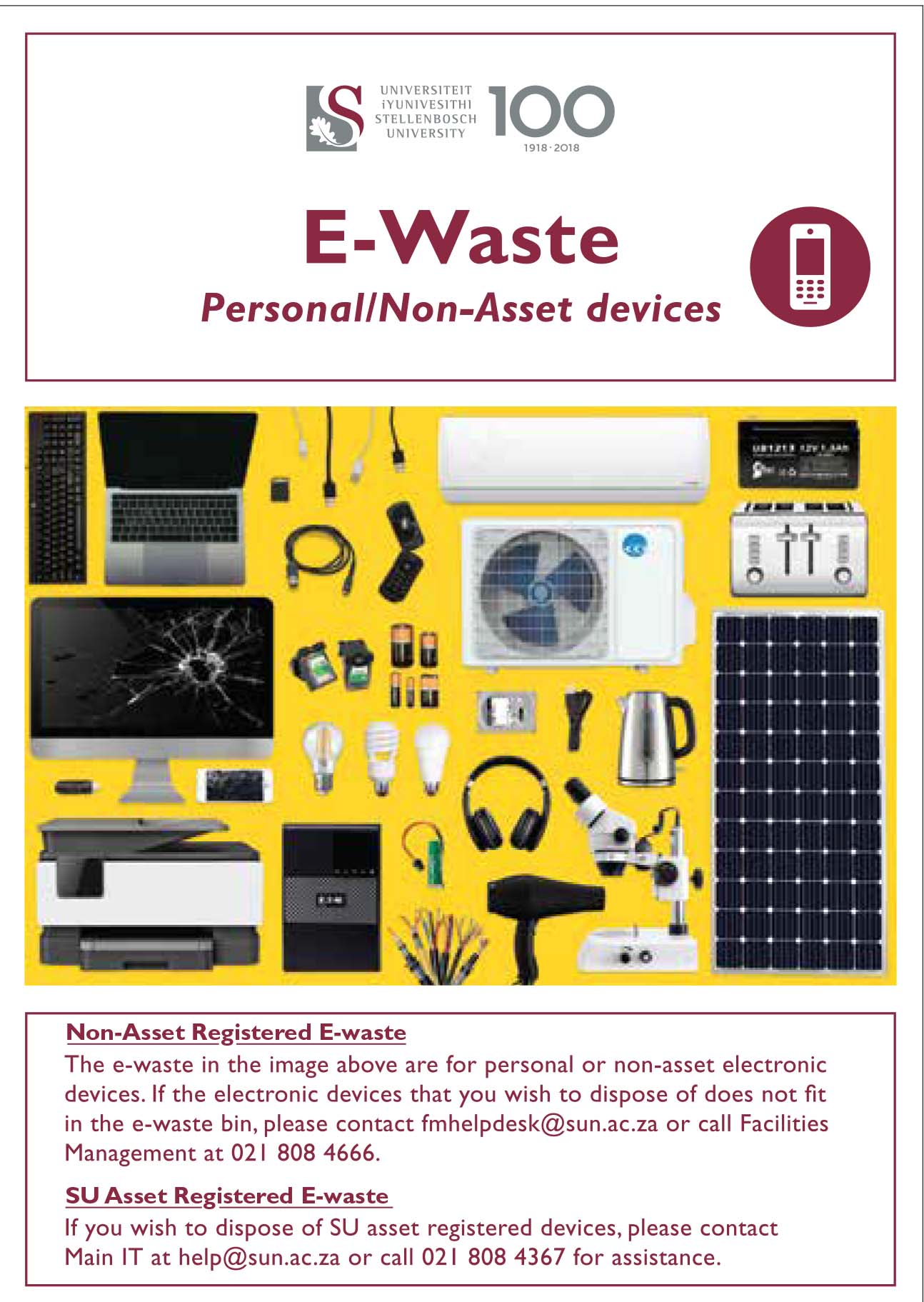
 As part of the campus “Going Green” project Facilities Management will be placing e-waste bins at selected spots on campus. We encourage staff and students to use these bins for any non-asset e-waste.
As part of the campus “Going Green” project Facilities Management will be placing e-waste bins at selected spots on campus. We encourage staff and students to use these bins for any non-asset e-waste.
Two of these yellow bins (see example right) will also be located at IT. A bin will be placed at the IT HUB by the entrance and a second one will be placed at the IT Main building in Hammanshand Rd at the service entrance (facing IT the door on your right) Both bins will be just inside the buildings by the doors.
WHAT IS E-WASTE?
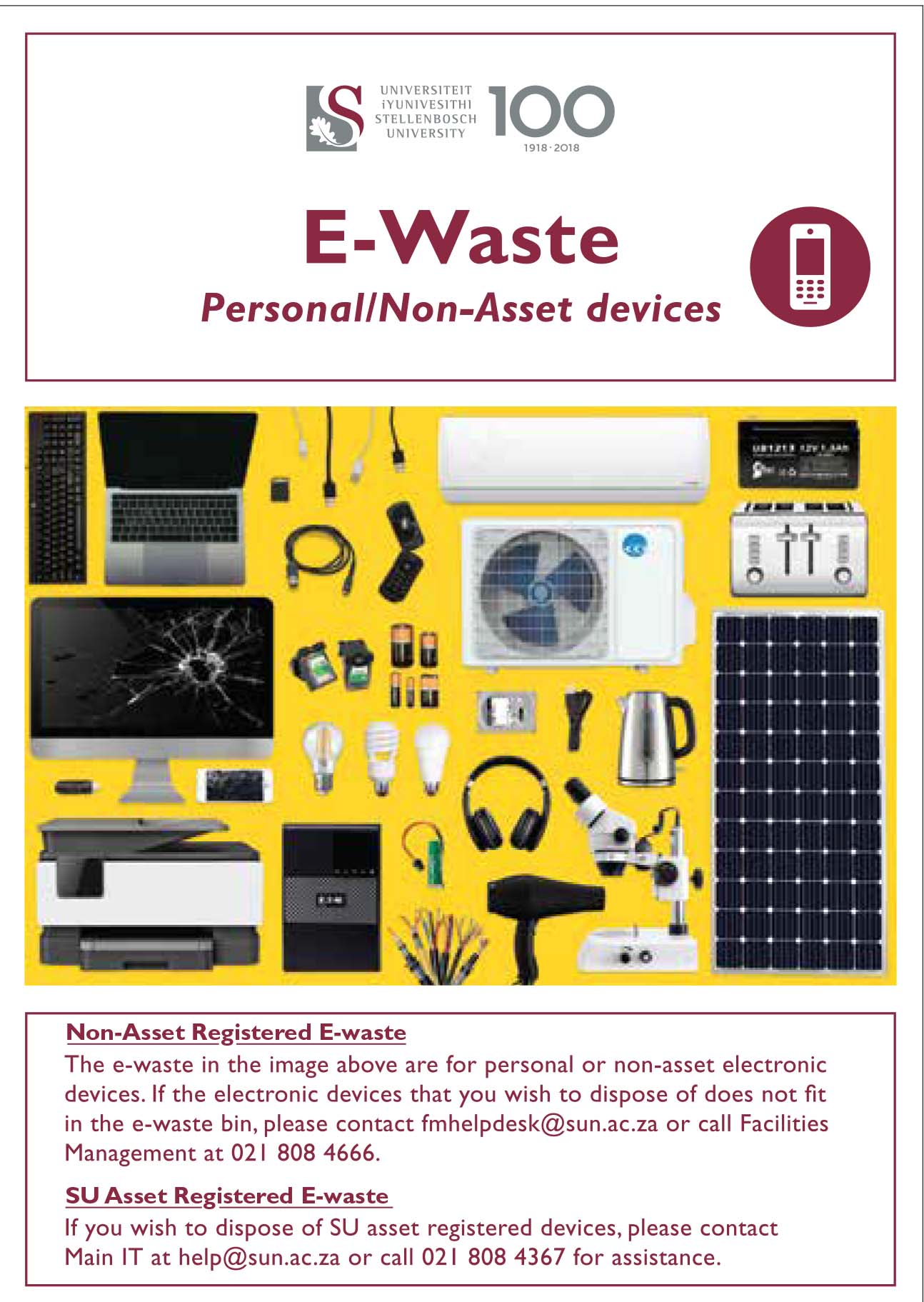
Electronic waste (e-waste) or Waste Electrical and Electronic Equipment (WEEE) are the terms used to describe old, end-of-life or discarded appliances using electricity. It includes computers, consumer electronics, batteries etc. which have been disposed of by their original users. More on e-waste.
We encourage all staff and students to use these bins for any non-asset e-waste. Bins will be serviced by Wasteplan and weekly inspections will be made by the university’s Wasteplan site supervisor to assess when a collection is needed.
For assistance and enquiries please email fmhelpdesk@sun.ac.za.
[:af]
 As deel van die “Going Green”-projek sal Fasiliteitsbestuur e-afval houers op uitgesoekte plekke op kampus uitplaas. Ons moedig personeel en studente aan om hierdie houers te gebruik vir enige e-afval wat nie US-bates is nie.
As deel van die “Going Green”-projek sal Fasiliteitsbestuur e-afval houers op uitgesoekte plekke op kampus uitplaas. Ons moedig personeel en studente aan om hierdie houers te gebruik vir enige e-afval wat nie US-bates is nie.
Twee van hierdie geel houers (sien voorbeeld regs) sal ook voortaan by IT wees. Een houer word geplaas by die IT HUB-ingang en die tweede sal geplaas word by die diensingang (die deur aan jou regterkant as jy voor IT staan) van die IT-hoofgebou in Hammanshandstraat. Beide houers sal binne die gebou geplaas word by die ingang.
WAT IS E-AFVAL?
Elektroniese afval (e-afval) is die term wat gebruik word om verouderde of weggooi-toerusting wat met elektrisiteit werk, te beskryf. Dit sluit rekenaars, enige elektroniese toerusting, batterye, ens. in wat uit die weggeruim is deur die oorspronklike eienaars. Meer oor e-afval.
Houers sal onderhou word deur Wasteplan en die universiteit se Wasteplan terreinopsigter sal bepaal wanneer die houers leeggemaak moet word.
Vir enige navrae oor die e-afval projek, stuur gerus `n e-pos aan fmhelpdesk@sun.ac.za.
[:]