Cyber security is the skill and ability of protecting networks, devices, and data from unlawful access or criminal use and the practice of guaranteeing confidentiality, integrity, and availability of information.
Communication, transportation, shopping, and medicine are just some of the things that rely on computers systems and the Internet now. Much of your personal information is stored either on your computer, smartphone, tablet or possibly on someone else’s system. Knowing how to protect the information that you have stored is of high importance not just for an individual but for an organisation and those in it.
Did you know that:
- As of 2021, there is a ransomware attack every 11 seconds, up from 39 seconds in 20191,2
- 43% of cyber-attacks target of small businesses, and they have grown 400 percent since the outbreak began
More tips and resources can be found here.
 The US government’s Cybersecurity and Infrastructure Security Agency has made a collection of tip sheets available for use. These downloadable PDF documents contain all the information you need to protect yourself from cyber security risks in a convenient, compact format.
The US government’s Cybersecurity and Infrastructure Security Agency has made a collection of tip sheets available for use. These downloadable PDF documents contain all the information you need to protect yourself from cyber security risks in a convenient, compact format.
- Cyber security starts with you
- Creating strong passwords
- Cyber security at the office
- Identity theft and internet scams
- MFA (Multi-factor authentication)
Also read more on MFA for Stellenbosch University staff and students on our blog - Online privacy
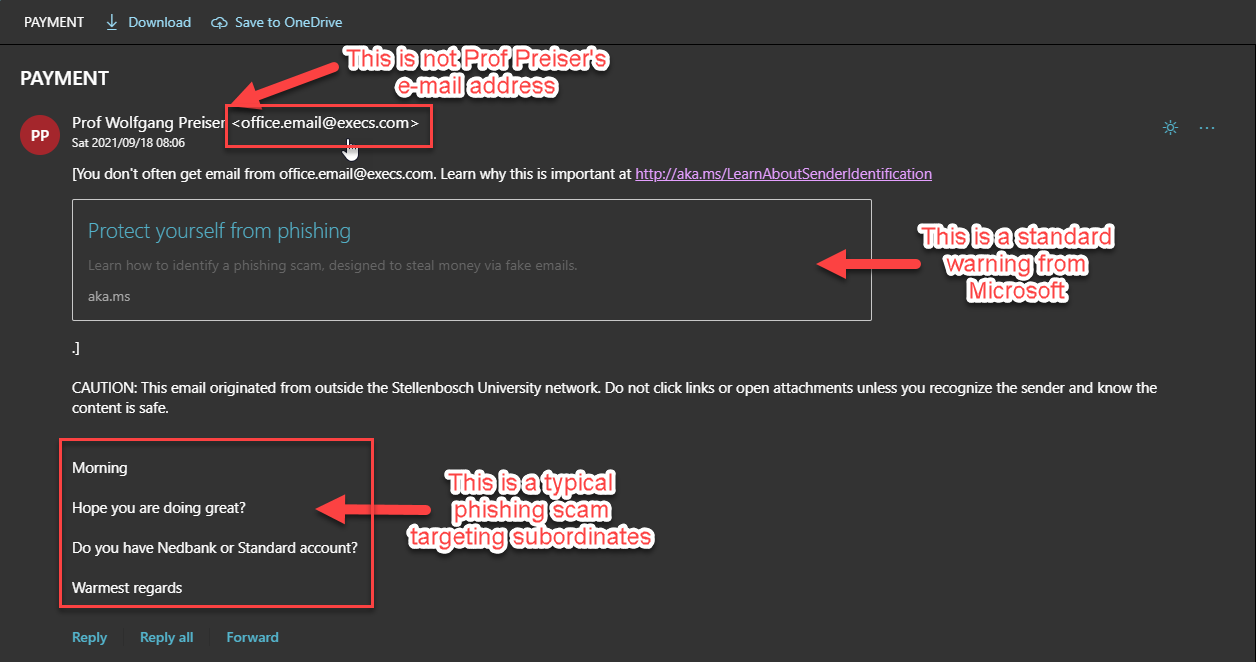
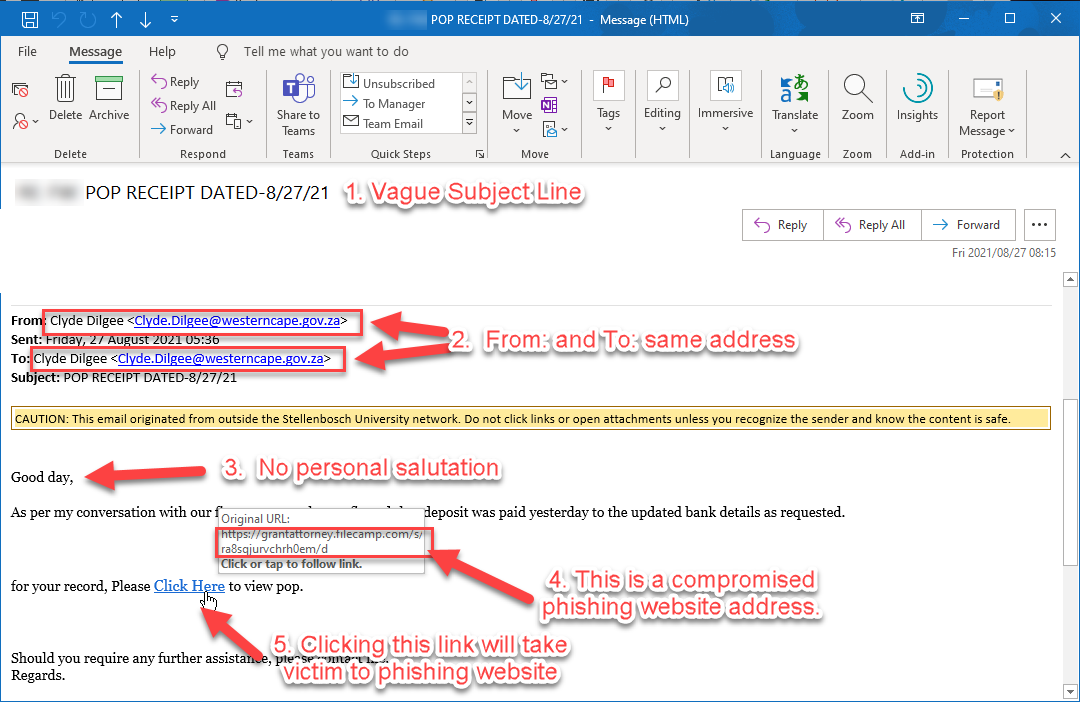
- Phishing and spoofing
- Protecting your digital home
- Cyber safety on social media
- Cyber security while travelling
More tips and resources can be found here.
[SOURCE: Cybersecurity and Infrastructure Security Agency, United States Government)


 Before
Before