In a previous article, we referred to “spear phishing“. Spear phishing attacks deliberately target the university instead of sending out general emails, hoping someone will respond. This approach is successful because scammers focus on typical staff and student activities and adapt their phishing emails accordingly.
In a previous article, we referred to “spear phishing“. Spear phishing attacks deliberately target the university instead of sending out general emails, hoping someone will respond. This approach is successful because scammers focus on typical staff and student activities and adapt their phishing emails accordingly.
Over the past two years, the university was targeted with a few large-scale spear phishing attacks resulting in student and staff accounts being compromised and in several instances, some of the victims suffered financial loss.
In April 2017 an e-mail was sent from “Stellenbosch Payroll” with the subject of “NOTIFICATION: Your 13.69% Salary Increase.” The bait of a 13.69% salary increase certainly attracted attention and was sent at a time when salary increases and performance bonuses were being granted.
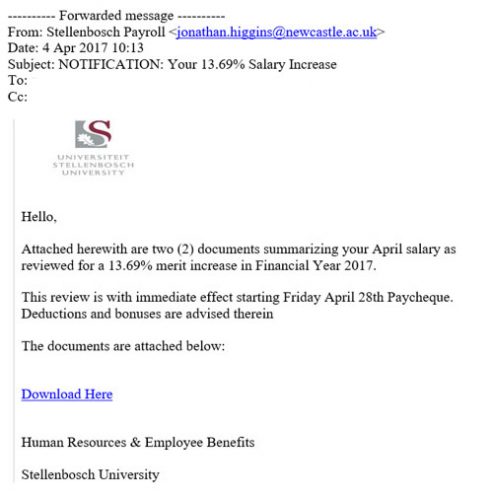 Many people overlooked the lack of a personal salutation and the grammar and spelling mistakes. The lure of a 13.69% salary increase and possible sizable salary increase made them throw caution to the wind. The university branding also created a false sense of security.
Many people overlooked the lack of a personal salutation and the grammar and spelling mistakes. The lure of a 13.69% salary increase and possible sizable salary increase made them throw caution to the wind. The university branding also created a false sense of security.
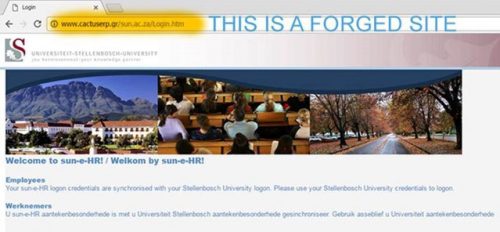
According to the email, staff had to download the two attached documents with information on the salary increase. University staff clicked on the links and was diverted to a forged website identical to the real login page of the University Human Resources division. The forged website address was not in the university domain but very few people would spot that detail. (see below)
Once on the site, they entered their usernames and passwords to view the documents explaining their so-called salary increase. The password did not work, but the scammers captured usernames and passwords and gained access to the real HR website using the stolen details and changed the victim’s banking account details so that their salary would be paid into the scammer’s own account. The person’s bank account details were also captured and could be for further exploitation.
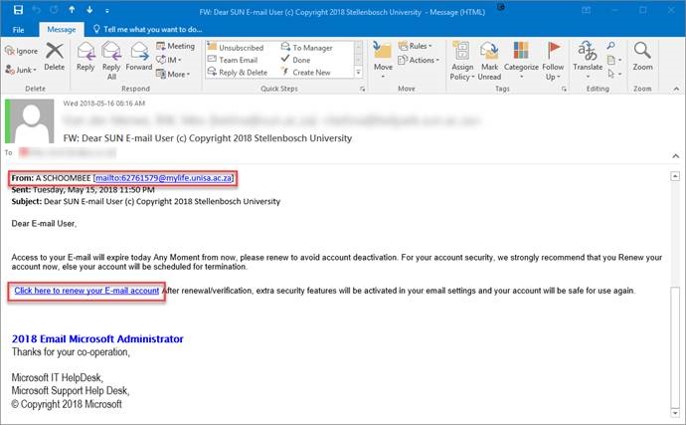
A second spear phishing attack occurred a year later in May 2018.
An email was sent from an already compromised UNISA account. The mail warned that the receiver’s email account was due to be deactivated and that they should click on a link to renew it. The Subject said “Dear SUN E-mail User (c) Copyright 2018 Stellenbosch University” and the signature was from the “2018 Email Microsoft Administrator”, which many saw as legitimate.
Clearly, the spear-phishing scammers researched their intended target and used words and other details like SUN, Stellenbosch University & IT HelpDesk that would increase its legitimacy.
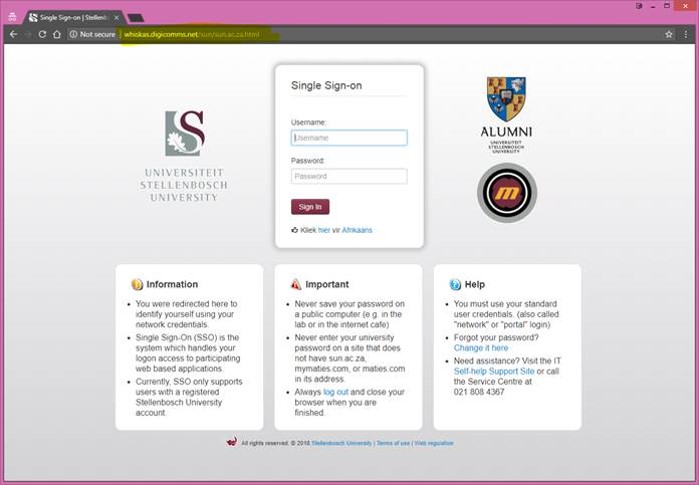
The link took the victims to another forged website. This time it was a perfect copy of the University’s own “Single Sign-On” page students and staff use to access important University services, for example SUNLearn and the staff portal. (see below)
The website address was also not in the university domain, but the rest of the details, such as the branding and the Afrikaans link, looked convincing.
Once the victims entered their usernames and passwords, the scammers gained control over the user’s accounts and could send out further email messages from within the university to catch more victims.
What could we have done to spot and prevent these attacks?
Unfortunately, there is an institutional perception that Information Technology has to prevent and protect users against attacks. This is not true. Users of an institutional network or even private users have the responsibility to be aware of the dangers we face in cyberspace, to sensitize themselves to the warning signs, be informed and help Information Technology flagging suspicious e-mails by reporting them and not using weak or easily-guessable passwords.
Here are some common-sense checks:
- Don’t trust display names. These can be anything a scammer wants them to be.
- Check for fake email domains. These will often be slightly different versions of the real thing.
- Look at the university logo and other images. Are they commonly available on the internet?
- Review links carefully by hovering over the link text (without clicking). A link that is different from the one in the link text is a sign that it is malicious.
- Look for the sun.ac.za domain name in the link. If the domain is different it is probably a malicious link.
- Look out for bad spelling and grammar, as this can be a tell-tale sign that it’s not a legitimate message.
- Spear phishing emails and messages are highly focused and targeted. The criminal will spend a lot of time compiling emails and website to look authentic.
- If you are suspicious about an email don’t visit the site. Verify it first by checking with Information Technology if it’s legitimate.
- Use strong passwords and never use the same password (especially if it is a weak one) on multiple sites.
In the final article for the Cybersecurity Awareness Month, we will share a few thoughts on how to increase your cybersecurity awareness and give a few tips and suggestions about what the university could do to fight and prevent these attacks.
Keep safe out there.
Tags: phishing