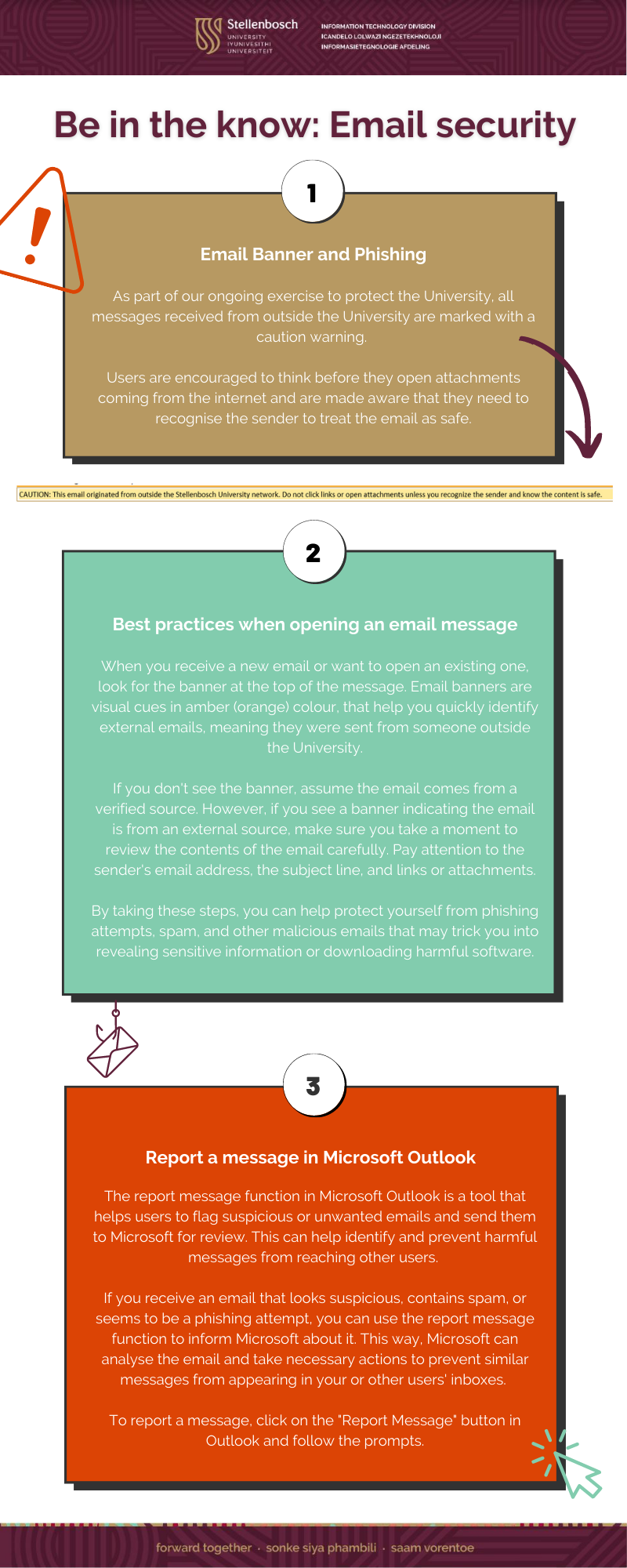
View a PDF here: Phishing and Report Message Infographic
View a PDF here: Phishing and Report Message Infographic
This article was compiled by Elnita Jacobs, Computer Technician 1: IT General Support Services, and Bradley van der Venter, Senior Configuration Specialist: IT General Support Services.
In today’s world with the ever-changing threat landscape, keeping our devices up to date is essential for ensuring they run smoothly and securely. Windows Updates is one of the most critical updates we need to keep up with.
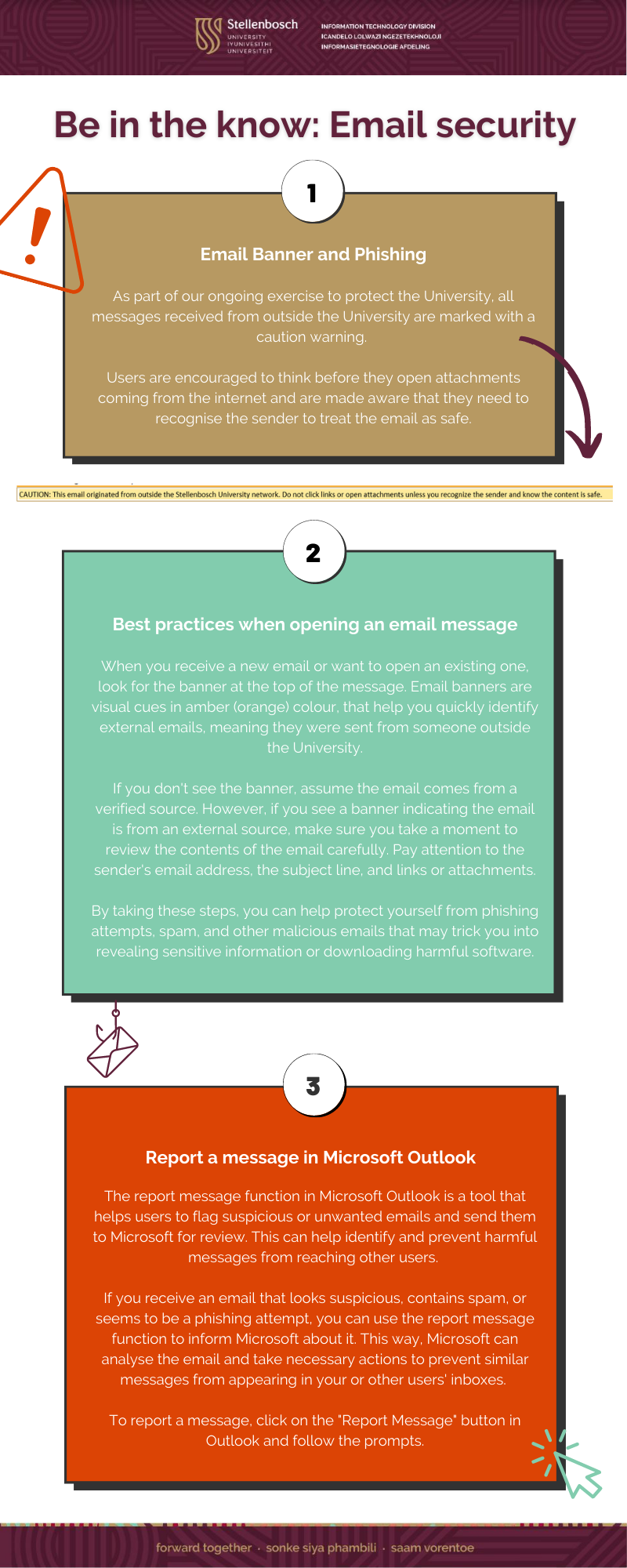
1 – The Importance
Firstly, let’s talk about why installing Windows Updates is so important. These updates are designed to fix bugs and vulnerabilities in the operating system, improve performance, and add new features. This means that by installing updates, you can keep your device running smoothly and securely and take advantage of new features that Microsoft releases. Windows Updates can also help to protect your device from malware and other security threats, making them a critical part of your device’s overall security.
2 – “Patch Tuesdays”
It’s also worth noting that Windows Updates are typically released on the second Tuesday of every month, known as “Patch Tuesday”. This means that by default, Windows Updates are enabled to install automatically, and you can expect your device to receive updates shortly after this date each month. Additionally, if you fail to restart your device after updates have been installed, Windows will force a restart after seven days to ensure compliance.
Please note that this is not enforcement from Stellenbosch University (SU) but from Microsoft.
This is important to keep in mind, as it ensures that your device stays up-to-date and secure, even if you forget to restart after installing updates. For example, suppose you restart your device immediately after updates are installed. In that case, you minimise the risk of, for example, being in a meeting and then Windows notifying you that it will restart in approximately 20 minutes.
This will only happen if you haven’t restarted your device for more than seven days after installing the Windows Updates.
3 – The Consequences
Now, let’s consider the consequences of failing to install Windows Updates. First, when you fail to update and restart your device, you leave it vulnerable to security threats. Hackers can exploit the operating system’s vulnerabilities to gain access to your device and steal sensitive information such as passwords and financial data. Malware can also infect your device, causing it to slow down, crash, or render unusable. Additionally, failing to update your device can result in poor performance, as bugs and other issues can accumulate over time, making it harder to use your device efficiently.
One of the most significant risks of not updating your device is the possibility of data loss. If your device becomes infected with malware or crashes due to bugs, you may lose important data such as documents, photos, and videos. This can be devastating, particularly if you have not backed up your data. Additionally, if you use your device for work, you may risk losing valuable business data, which can be catastrophic for your business.
4 – The Solution
What can you do to ensure that you are keeping your device up to date? The simplest solution is to enable automatic updates on your device (Stellenbosch University Windows Asset devices joined to the domain have this enabled by default). This will ensure that your device receives updates as soon as they become available without any effort on your part. Alternatively, you can manually check for updates by going to the Windows Update in the Settings option on the Start Menu. Restarting your device regularly after installing updates is also important, as this ensures that they are fully installed and can take effect.
In conclusion, installing Windows Updates is crucial for ensuring your device runs smoothly and securely. By keeping your device up to date, you can take advantage of new features, improve performance, and protect yourself from security threats. Failing to update and restart your device for updates can lead to poor performance, data loss, and security vulnerabilities. So, ensure you enable automatic updates or manually check for updates regularly, and always restart your device after installing updates.
Reference:

Universities around the world are facing ever increasing cybersecurity risks, particularly in the post-pandemic world – and Stellenbosch University is not immune to these threats. Even before Covid-19 struck, higher education institutions were already gathering vast amounts of data from students and staff – and now, with more hybrid and remote offerings, requiring even more information, the risks of cybersecurity have become massive.
The risks for these data rich institutions are wide ranging and include ransomware attacks, business email compromises, data and privacy breaches, as well as adversary-in-the-middle attacks, said Brian Mhembere, the Cybersecurity and Technology Risk Specialist in the ICT division at Stellenbosch University.
Brian, who has a background in IT in the banking, mining, health and financial services sectors, has seen and heard it all when it comes to cybercrimes. With his finger on the pulse of global cyber trends, and with first-hand experience of the havoc that cyber fraud can create, he has, in the past, been asked to share his expertise in interviews on television and on radio. He was even interviewed on the 8pm news on ETV ahead of Black Friday, where he warned South Africans of all that can go wrong when shopping online.
Now, as a key cyber “sleuth” at Stellenbosch University, he’s determined to ensure that the valuable student and research data stay safe.
“There have been a lot of data breaches in higher education institutions mainly through phishing attacks – attacks aimed at compromising personal identifiable data or to reveal personal sensitive information like credit card numbers, bank information or passwords,” he said in an interview.
Brian explained that ransomware attacks take place when a cybercriminal threatens to use technology to either publish or permanently block a victim’s personal data unless a ransom is paid. A data breach is a security violation, in which sensitive, protected or confidential data is copied, transmitted, viewed, stolen or used by an individual unauthorized to do so.
An adversary-in-the-middle attack is when an adversary intercepts communication channels between two components, with the aim of either altering the message or data, or compromising the integrity of the data a person is trying to transmit, with the result that the message reaches the intended recipient with altered information or configuration.
Brian was responsible for the recent cybersecurity maturity assessment and report on cybersecurity at the campus. The analysis was done using the ISO27001 standard and the National Information Security Technology (NIST) cyber-security framework, which uses a Capability Model Maturity (CMM) tool to analyse where the weaknesses lie in the whole IT environment. The CMM tool guides the analysis of the entire IT environment with controls mapping and scoring exposing gaps, in accordance with the ISO/IEC27001 standards.
“The report did not find anything out of trend with most universities around the world,” Brian said. “Our university falls in line with the current state of cybersecurity maturity of most other South African universities. There is still some work to be done to improve the cybersecurity of all these institutions. Our maturity is very low compared to universities in the UK and America, but better than that in some other countries in Africa.”
He said the audit was conducted during April and May 2022 and the report has not yet been published or made public.
“Even if we knew the findings, we would not make them public, because anyone who reads this article would know what our weaknesses are,” he said. “Even if SU had ever had an attack, we would not speak about it in the public domain. There have been attempts but we are able to monitor and protect most attacks.”
Brian said the issue of cybersecurity at the university keeps him on his toes, but this is nothing new. “When I was working as head of IT in one of the major private hospital groups, we had an incident with ransomware called Wanacry. One of our managers’ PC was encrypted by the hackers as she clicked on an attachment sent by email which contained some malicious code. Luckily, my office was right next to hers. I was able to run through and I saw her computer countdown times which said they were encrypting all her data on the computer unless she sent an amount in Bitcoin.
“We managed to quickly isolate her workstation and to disconnect it from the Internet, but it was too late to avoid the encryption on that workstation. However, we managed to prevent it from propagating through the network. We lost all the data on her machine, but because we had a good business continuity plan, we restored the data on her machine from our backups.”
In a humble deflection of his own vital role, Brian said: “This colleague saved the day. She followed all the awareness products we were pushing which is a major thing, as users are first and last in the line of defence. I have always placed a huge emphasis on user awareness and on campaigns to create what we call the the human firewall against cyber fraud.”
Brian, who grew up in Harare, Zimbabwe, has always been intrigued with information systems. He completed a Bachelor of Science, Honours degree in Information Systems, Diplomas in Telecoms Engineering, and Networking whilst working in various sectors. He is a Certified Information Security Manager from Information Systems Audit and Control Association (ISACA) and has since completed a range of other cybersecurity certifications and, in 2018, completed a Masters in Information Systems from the University of Cape Town.
“This is really very interesting work, as well as being very important,” he said. “In the age of digital transformation, everything is moving online and onto the cloud. It’s exciting to be part of this huge transformation and to educate users on best practices.
“Of course it keeps me up at night,” he said, of his role at Stellenbosch University. “But thankfully, our current chief director of IT has prioritised cybersecurity at the campus. We both recognise how important it has become in today’s world, especially for universities relying on remote working which was necessitated by the pandemic.”
He said the IT division is assessing the findings of the university’s audit into cybersecurity and is now working on implementing the recommendations from the report so as to strengthen their security and control in the digital sphere.
Brian said he tries to keep up to speed on cybercrimes, locally and internationally. “Recently, Uber was hacked. There were data breaches, and the matter is still under investigation. Each incident teaches us lessons. We learn how they were compromised, what their vulnerabilities were – and we compare this with ourselves. We ask ourselves, ‘if this happened to us would we be able to defend ourselves?”
He also cited numerous recent articles on the subject of cybersecurity, particularly in higher education. Part of his job, he said, is to keep up to speed on all developments in cyber fraud, which involves reading research, articles and journals on the subject. During the interview, he gave figures and case studies from various studies, including the Bank of America, Checkpoint, Sophos and Verizon.
“For example, the IT security company, Sophos recently published its report, The State of Ransomware in Education 2022 in which they gave insights into the ‘ever more challenging attack environment’ in which the education sector finds itself,” he said.
“Key findings are that ransomware attacks on education have increased – 64 percent in higher education were hit in 2021. Education is the sector least able to stop data being encrypted in an attack – higher education reported the highest data encryption rate of all sectors at 74%.
“The study also found that … education has below average cyber insurance coverage rates – only 78% of education organisations have cyber insurance coverage against ransomware compared with the global average of 83%. Many education organisations are choosing to reduce the financial risk associated with such attacks by taking cyber insurance.”
Cybersecurity should be a priority project for SU, Brian said. “So much could go wrong when a university is targeted. For example, when data breaches happen with student admissions and other personal data, a university can be fined by the regulator in terms of the POPI act. If our systems are compromised, the university could be forced to pay a breach fine of up to R10 million – or ten years in jail.
“We need to be always searching for the gaps. Hackers work 24/7 and always come up with new ways to compromise and breach systems for corporate espionage, financial gain, or national security espionage. We have to keep abreast with what’s happening in the world as it filters back to us.
“I’m so glad that SU’s senior management has bought into the importance of cybersecurity. To have an organisation with a chief director of IT who gives her full support – from budgetary support to moral support – on the importance of cybersecurity is hugely valuable.”
Image credit: Thomaguery; Getty

A student is innocently going through her emails. She sees one from a person she’s never heard of. There are spelling mistakes, but she ignores them and clicks on an attachment in the email. Suddenly her PC locks down and she can’t access her files. A message comes up and tells her she has to pay money to get her PC unlocked. Her data is kept ransom.
A use case from another university is a payroll supervisor logging into a public network at a hotel to check his emails and finalise the payroll. Later that evening he checked his email only to discover replies and emails from individuals he didn’t contact. His credentials have comprised and when he tried logging in again, he could not, staff salaries, personal information about staff all in the hands of a criminal. He was the victim of key locking.
These are real life examples of what can go wrong when a university is subjected to a cyber-attack. According to Dr Zenobia Davidse, IT Director General Support Services at SU, research shows that there has been an increase of 485% in ransomware threat level (Consumer Threat Landscape Report) and cyber-attacks are the fastest growing crime.
“These are picked up by the advance threat protection that is in place to detect them, and, thanks to efficient systems in place, they are averted, but it is still critical for all students and staff to play their part in ensuring the university’s safety against cyber-attacks,” Dr Davidse said in an interview.
“There are practical habits which everybody on campus can adopt to ensure safety against cyber-attacks,” she added.
In her position as IT director, Dr Davidse is in charge of “providing a set of services to assist, coordinate and support IT activities across the broader ICT function of the university”. Part of the task is supporting strategic initiatives across the campus.
A key task in her portfolio is the communication across campus about IT developments and threats.
Dr Davidse said there are a number of things which staff and students do which can put the university at serious risk – and these are often inadvertent actions. “Leaving your student card lying around is an invitation to gain access to SU buildings; failing to protect the password for your computer is also a big mistake; responding to a suspicious email, SMS or whatsapp is a no go – and even downloading a recording of a Teams meeting sharing the file with someone who should not have access to the information, can be serious repercussions for the university,” she said.
“Cyber criminals are constantly on the prowl for student information, data that they can exploit, systems they can keep at ransom – and they have very clever ways of getting it.”
Dr Davidse said there are a few things students should know when using the systems on campus. “It is important to be cautious when they log into the university’s various systems. Our correspondence to students would not be a request to fill in their username and password. So, if you receive any email, SMS or whatsapp from someone saying they are a representative of the university, and they need your password from you, you should not respond.”
Elaborating, she said: “A student’s access card is like a bank card because it enables access to different buildings, it contains printing credits, washing quotas, meal subsidies, etc, so if you leave it lying around, you can enable criminals to get access to places where your card has been provisioned for or deplete the credit.
“Another no no is to type your password out and paste it against your screen; or to share your password with someone else. Another action which is potentially dangerous is when staff create a shared folder and give people access without understanding that there is confidential information in there which others are not allowed to see.”
Dr Davidse said the university has a system in place to inform students which emails come from inside the university and which come from outside. “People should not ignore the ‘external’ sign that pops up in an email. Sometimes, you get an email, and you don’t know the person who sent it, but, out of curiosity, you click the link, start filling in a form or something and it is only then that you think, ‘but, why would the university ask me these things?’ Often it’s too late.”
Asked for practical examples of how students and staff can help to cyber-secure the university, Dr Davidse said: “A practical example is to use very secure passwords. Use a combination of lower and upper case letters, as well as numerical and alpha numerical – and never use the same password across different platforms. Do not use your university email address for a social media platform.
“Phishing emails and installing malware are methods used to gain access, trick someone share the username and password.”
Asked how staff and students can report cybersecurity risks at SU, Dr Davidse said the university has two very effective mechanisms. “One is to report the risk to the email, csirt@sun.ac.za, which is an email we use specifically for cyber incidents for prioritisation by our team.
“We also have a reporting utility within our email client. If an email comes in, there is a reporting functionality, allowing you to ‘report this message’ which you can do.”
Dr Davidse, who finds her job both challenging and fascinating, loves what she does. “I started off studying engineering. The most fascinating thing about engineering is to see how software can bring an idea to life; you see the promises of technology coming to fruition and the beauty of how it can really make things better in the world. I love how the answer is never obvious. You must do quite a bit of work before you find the solution to an issue.”
The best part of the job – which also involves linking the latest technology to the realm of higher education – is that it is constantly changing. “You can be finished with implementing one technology and the next piece comes out making it more advanced and innovative, so it’s never boring.”
Her last word, on cybersecurity, to students and staff, is: “People are trying to hack into systems all the time. It is up to all of us to protect our institution from this by putting simple measures in place and being constantly vigilant.”
Image credit: Guvendemir; Getty

About six years ago, when Dr Denisha Jairam-Owthar was working as Chief Information Officer for the City of Johannesburg, the city was subjected to a massive cyber-attack which brought the organisation to a grinding halt. Hackers got into the city’s network and demanded money. The metro – the biggest in South Africa – had to switch to disaster recovery mode and all systems had to be shut down.
“That was when I experienced, first hand, the magnitude of a cyber-attack on this scale,” Dr Jairam-Owthar said.
“When this sort of attack happens, the whole technical team faces a mammoth, urgent task. You have to look at every single system and find out where the vulnerability was. While you’re doing all this, you must ensure the organisation can continue to operate. This must all happen in parallel. There is no level of tracking or planning on paper that can prepare you for that day.”
At the time of the cyber-attack, Dr Jairam-Owthar had a four-month-old son. But that didn’t stop her from joining her team in working a gruelling 90 hours a week. “My staff and I brought sleeping bags so that we could sleep at the office, working shifts, sleeping for three or four hours at a time, manning our nerve centre to technically unravel this cyber-attack.” Her baby became sick from not seeing his mum, and the paediatrician asked what was happening at home. She explained that she was dealing with a crisis – and had no option but to soldier on.
Fast forward to today – and, as Stellenbosch University’s Chief Director: Information Technology Division, Dr Jairam-Owthar is always, on high alert for cyber-attacks on the campus. “Cybersecurity is one of those things that keeps me awake at night,” she said.
In an extensive interview, Dr Jairam-Owthar (39), who took up the position in January this year, was reassuring that SU is in safe hands. But with risks always at play, she stressed that cybersecurity should be “everybody’s business” on campus.
“Cybersecurity is a hot topic, because it is becoming increasingly prevalent. We see cyber-attacks on prominent organisations on a daily basis. They might have all the controls in place, but it just takes that one vulnerability to probe the weakness to come through – and before you know it, the entire network has been permeated. It is not a matter of if a cyber-attack is going to happen … it’s a matter of when,” she said.
“CIOs have no option but to ensure that their cybersecurity systems are well resourced and resilient. The cost impacts on organisations and on society as a whole can be very difficult to come back from. Every CIO must be ready for when this happens and know how to respond – on a technical level, and on other levels, like how the institution deals with the situation.”
Dr Jairam-Owthar said the Covid-19-driven switch to digital acceleration has contributed hugely to the growth in cybercrime. “So many people suddenly found themselves working from home and depending on digital platforms. Cyber criminals quickly understood they could exploit this situation. Hackers are also highly aware that, in developing economies, many institutions do not update and upgrade their technology and infrastructure, and that’s where the vulnerability sits. These very intelligent hackers know we are challenged with funding, to keep up with technology. This is why countries in Africa become targets.”
Moving to why cybersecurity is so important for SU, she said: “This is an institution of real excellence in academics and research. We have researchers across many faculties, and there is so much research data in the system. Ethics in research is so critical. You cannot release the data unless you have followed all the processes. It is absolutely vital to ensure that the data, network and our online systems is well secured.
“On top of this, the system contains a great deal of students’ personal information – their exam marks, certificates and their whole student life cycle information. This could all be affected in a cyber-attack. When an attack happens, the reputation of the entire university comes into question, and those who fund research could become sceptical.
“I have to be able to say to my bosses at SU, hand on heart, that I’ve done everything I can to protect all our systems, network and information.”
Giving strong reassurance that SU is in safe hands, Dr Jairam-Owthar said cybersecurity was high on her agenda when she joined the university in January. “With the support of the university’s leadership, we did an assessment of where we stand. It found that we are well within the industry norm but there’s a lot more to do because, when it comes to cybersecurity, we are faced with a moving target. We cannot be static or complacent about it. So while we are fine in terms of the industry norm, we have to always drive to improve. The most critical challenge for CIOs is to keep up with this moving target of cybersecurity.
“We do have our controls in place as a university, but … even if we put in excellent controls; someone in Amsterdam for example can find a vulnerability. We have to be on the pulse, staying ahead of the target – because it is moving all the time.”
Dr Jairam-Owthar said there is also the issue of balancing costs. “Our partnerships with our vendors, such as Microsoft, become critical. We have to consistently ensure our vendors deliver value. The skill lies in balancing shrinking budgets with moving targets and higher expectations of technology.”
When she was at the City of Johannesburg, Dr Jairam-Owthar played a key role in the institution’s IT Digital Transformation. Passionate about education, she believes her role at SU is to enable education through technology at SU, because IT is a ‘critical enabler’ in the transformation of education”.
“The impact of what we do is to enable students and staff to be educated. That is the part that speaks to me as a person. Education holds a place in my heart.”
Dr Jairam-Owthar said the university recently did an analysis using the National Information Security Technology (NIST) cybersecurity framework.
“The NIST is a tool which does a full analysis of the entire IT environment and where the weaknesses lie, and how to prioritise to close the gap. That report has been done, and we are engaging on it in terms of priority and the budget to start implementing it to strengthen our controls and security,” she said.
Turning back to the incident at the City of Johannesburg, Dr Jairam-Owthar said it was “like walking through fire”.
“It’s like having an intruder in your home, and you are standing in the house and you don’t know which door the intruder came in. I never want anyone to go through that again. I wouldn’t wish it on anyone. We need to be well prepared.”
Asked what her main message to SU students and staff is when it comes to cybersecurity, she said:
“My main message is that cybersecurity is everyone’s responsibility, not just that of the IT Division. Everyone on campus – staff and students – need to play their role. To stress the importance of this, we will soon launch our cybersecurity training aimed at strengthening our human firewall which is the staff and students. Everyone on the campus, must do their bit to strengthen this human firewall.
“SU has such excellence in academia and research. Let’s work together to find the gaps and strengthen the systems. It’s the simple things like don’t share your passwords, make sure you authenticate when you get on the network, don’t go to sites that look odd; being able identify a phishing email. Check with us if you are not sure. If you get an email that doesn’t sound right, talk to us and we will guide you. Most cyber-attacks come through the human firewall. We cannot work in silos for cybersecurity either. We need a holistic approach for SU for cybersecurity. Lastly, make sure you do the training, it will empower you on what to look out for.”
When Dr Jairam-Owthar looks at her son, now a healthy, happy hi-tech six-year-old, she sees a boy who “handles a phone, an Ipad and a computer all at once”.
“It is for this generation that we need to bring the university into the digital fourth industrial revolution.
“I say to my IT staff that; our primary stakeholders are the 33 000 students and the 3500 staff of this university. I want to know what our primary stakeholders look for in technology so we can meet their demands in a safe and secure way, where we are also implementing a key principle of ‘security by design’ on any technologies we implement”.
Image credit: Formatoriginalphotos
© 2013-2025 Disclaimer: The views and opinions expressed in this page are strictly those of the page author(s) and content contributor(s). The contents of this page have not been reviewed or approved by Stellenbosch University.