
Academic work at a university entails that the student be exposed to the ideas, written material and other intellectual and creative material of others. The intention with academic studies is precisely that the ideas of both the lecturers and the students will be shaped and polished by others. At the same time, students ought to go further than what was devised, written and created by others; he or she should critically evaluate it, provide new and original input or syntheses, and apply these to contemporary and local studies of problems. This is where academic activity becomes satisfying at university level.
Naturally, lecturers can only evaluate the contribution of their students if the contributions of others are clearly distinguished. This takes place through acknowledged systems or the process of acknowledgement and referencing. If these conventions are not adhered to and the required recognition is not given, the basis of the academic work at a university is undermined. Plagiarism is committed when someone elseŌĆÖs work (words, ideas, creations) are taken over and passed off as the┬ĀwriterŌĆÖs own.
The university uses Turnitin to test plagiarism. Turnitin integrates with the Learning Management System (Webstudies or Ematies). (See more information below) Assignment links are created within the LMS which students use to upload their assignments to. The assignments submitted by students are stored in a┬Ādatabase┬Āused to check for plagiarism. This prevents one student from using another student’s paper, by identifying matching text between papers. Assignments are also be checked against web pages, books, newspapers and available journals on the net.
The University aims to ensure that mechanisms are in place that will enable lecturers to promote academic integrity and to eliminate plagiarism. The most successful approaches to dealing with student instances of plagiarism allow for a ŌĆśdevelopmental approachŌĆÖ, which implies that cases of plagiarism ŌĆō with the exception of serious cases ŌĆō be used as opportunities to instruct the guilty persons as to what is expected and how to handle information. In addition, such a student could be directed to redo the assignment.
For more information on the university’s the Interim Guidelines for dealing with Plagiarism, please visit the CTL website: http://stbweb02.stb.sun.ac.za/ctl/policies.html
Article compilied from the Interim approach to dealing with plagiarism policy┬Āby Marinda van Rooyen
┬ĀTURNITIN/WebStudies official website
TURNITIN Logon problems & Help
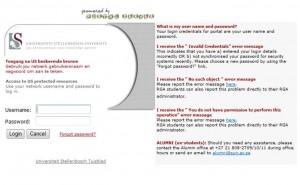
–┬Ā┬Ā┬Ā┬Ā┬Ā┬Ā┬Ā┬Ā┬Ā If you can’t log in to WebSTudies or Blackboard, Go to www.sun.ac.za/useradm ┬Āand change your password.
–┬Ā┬Ā┬Ā┬Ā┬Ā┬Ā┬Ā┬Ā┬Ā Any other WebSTudies or Blackboard related queries (modules not showing etc.), send an e-mail to WebStudies or Samuel Morris or
call+27(0)21 808-2443
┬Ā


 A task team (Johann Kistner, drs Antoinette van der Merwe & JP Bosman and ms Marinda van Rooyen) facilitated the evaluation, including consulations with academic, administrative and support services staff. The success of systems, as well as the scale on which they were used by other universities, were also looked at. In the end a decision was made based on a set of predefined, weighed criteria. The following was taken into account:
A task team (Johann Kistner, drs Antoinette van der Merwe & JP Bosman and ms Marinda van Rooyen) facilitated the evaluation, including consulations with academic, administrative and support services staff. The success of systems, as well as the scale on which they were used by other universities, were also looked at. In the end a decision was made based on a set of predefined, weighed criteria. The following was taken into account:
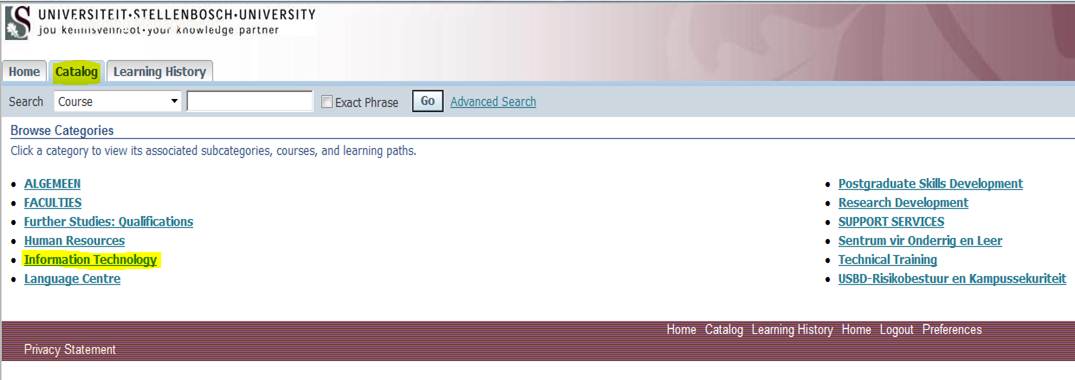
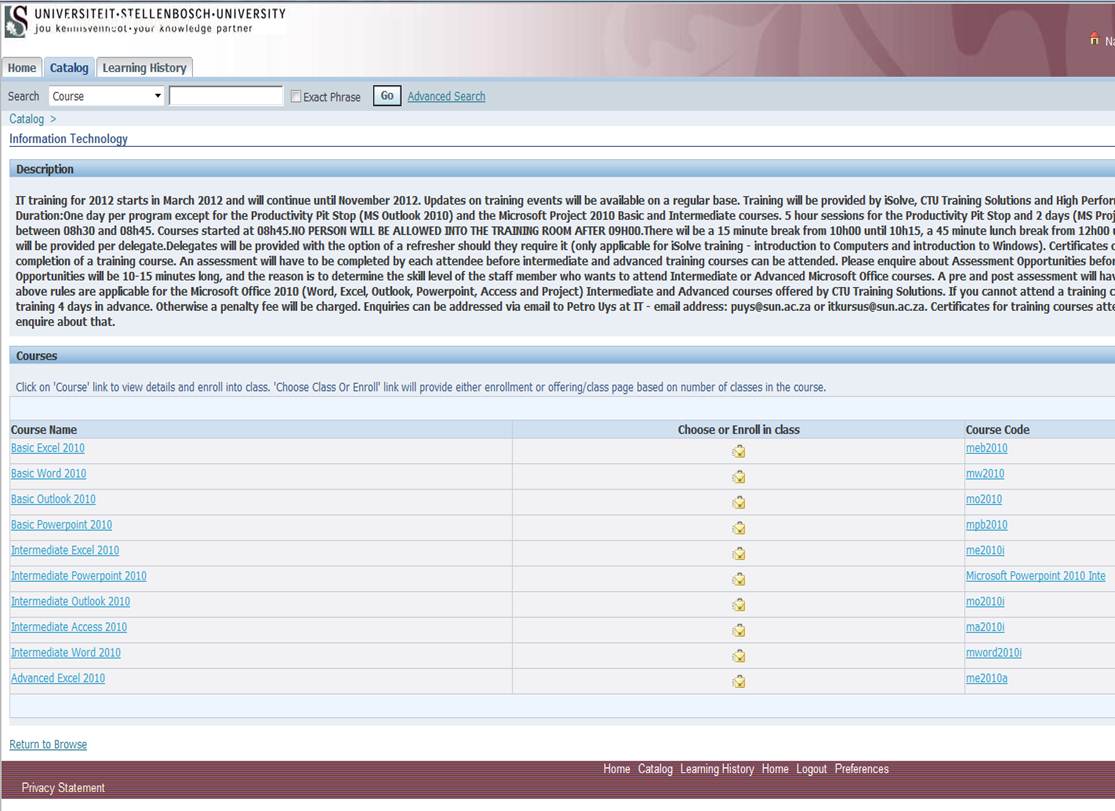
 Does a large portion of your day consist of managing projects and seeing to it that everything runs smoothly? Whether you are a project manager or just closely involved with projects within your department, MS Project could make your task easier.
Does a large portion of your day consist of managing projects and seeing to it that everything runs smoothly? Whether you are a project manager or just closely involved with projects within your department, MS Project could make your task easier.