How do I report an IT problem, request or enquiry?
Option 1
Log a service request on our ICT Partner Portal┬Āwith the following information:
1. Description of problem
2. Telephone number
3. Room Number
4. Department and building
5. Asset number of computer, laptop, printer, etc.
Requests will be logged automatically and reference number sent via email.
For video instructions on how to log a request on the ICT Partner Portal, click here. More information on our Service Catalogue.
Option 2
Contact the IT Service Desk ŌĆō 021 808 4367
We require username and asset number in order to assist OR leave a voicemail message.
How do I follow up on the IT request I have logged?
Whether you have called the IT Service Desk at 0218084367, sent an email to help@sun.ac.za or logged a request via the ICT Partner Portal at https://servicedesk.sun.ac.za you can do the following:
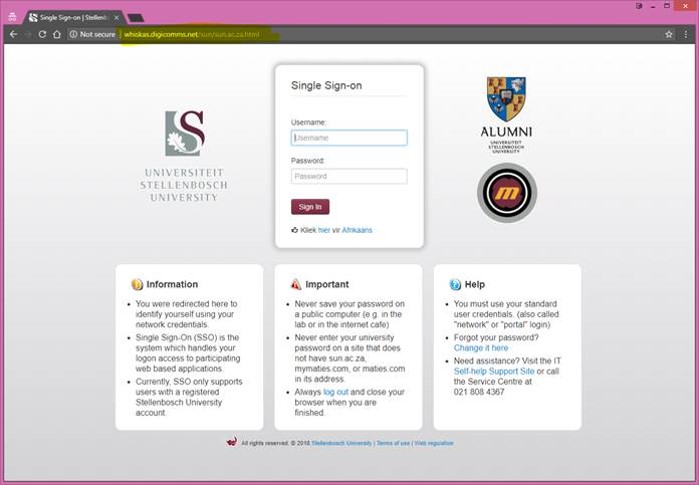
- Log in at https://servicedesk.sun.ac.za with your username and password.
- Select: Requests, My requests. The status of all the requests that you have raised will be displayed.
How do I follow up if I sent an email to help@sun.ac.za?
If you send an email to help@sun.ac.za it automatically logs a request on the IT Service Portal. You can check on the status of your request as follows:
- Log in at https://servicedesk.sun.ac.za with your username and password.
- ┬ĀSelect: Requests, My requests. The status of all your requests will be displayed.
How do I follow up on a request I reported by calling the IT Contact Centre?
If you call the IT Contact Centre, the service agent will log a request on your behalf on the IT Service Portal. You can check on the status of your request as follow:
- Log in at https://servicedesk.sun.ac.za with your username and password.
- Select: Requests, My requests. The status of all your requests will be displayed.
Can you follow up on a request emailing help@sun.ac.za again?
If your request have already been logged and you have a reference number, please do not send another email to help@sun.ac.za. This will log a second, duplicate request which will only clog up the system and cause confusion. The same goes for replying to emails from help@sun.ac.za. Rather click on the request number and add your comment on the system.
How do I add a comment to my request?
- Log in at┬Āhttps://servicedesk.sun.ac.za┬Āwith your username and password.
- Select:┬ĀRequests, My requests.┬ĀThe status of all the requests that you have raised will be displayed.
- Click on the reference number of a request to see its details.
- Type your comment in the text box and click on┬ĀAdd.┬ĀThe comment will be added to the request. You can also add screen shots for clarification
What does the different status options mean?
WAITING ON SUPPORT =you are waiting for a response / feedback from IT regarding your request.
WAITING ON CUSTOMER =IT is waiting on a response / feedback from you regarding your request.
IN PROGRESS = your request is being attended to.
ESCALATED =your request is escalated for further investigation.
RESOLVED =your request has been resolved.
CLOSED = your request has been closed.


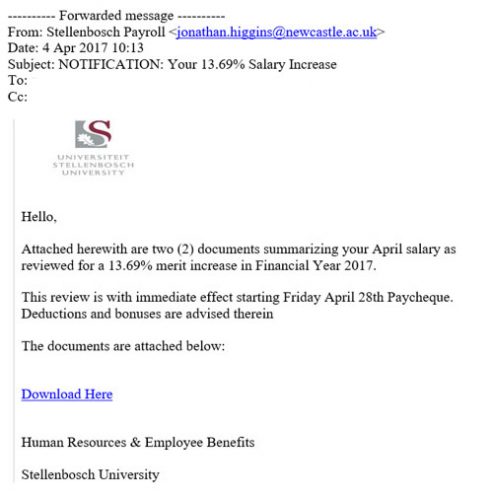
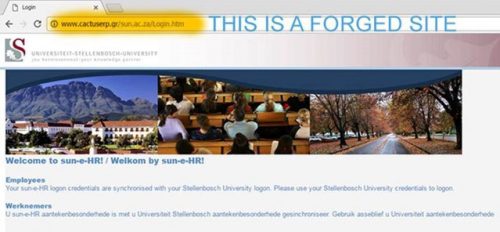
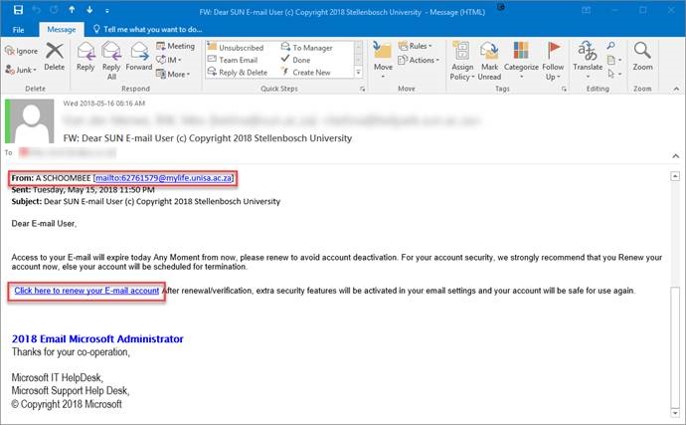
 For a large enterprise like Stellenbosch University phishing attacks are the most common cybercrime.
For a large enterprise like Stellenbosch University phishing attacks are the most common cybercrime.