Computer and Digital Literacy are two separate things, but they go together. For us to be effective, responsible technology users, we need to have both. In this article we explore the difference between these two concepts, and why it is important to develop digital literacy skills.
What is computer literacy?
Computer literacy is defined as the knowledge and ability to use computers and related technology efficiently, with skill levels ranging from elementary use to computer programming and advanced problem solving. Those who are computer literate have┬Āthe ability to perform basic tasks on the computer. For example, switching on your computer, knowing how to access the internet, navigating a browser, and operating software systems, and completing any other tasks that make it possible to do your job.
What is digital literacy?
Digital literacy is the ability to navigate our digital environment using reading, writing, critical thinking and technical skills. ItŌĆÖs about using technological devices such as a smartphone, laptop or tablet, to find, evaluate and communicate information. So, digital literacy goes beyond computer literacy because it gives individuals the power to connect around the world.┬Ā
Why is digital literacy important?
Digital literacy skills are essential for participating in the modern economy. Digital literacy can play a powerful role in helping people connect, learn, engage with their community, and create more promising futures. Simply reading articles online does not address digital literacy, so it is important for everyone to understand the variety of content and possibilities that are accessible online.
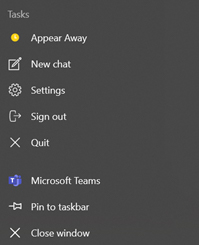
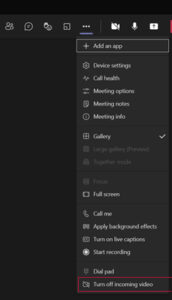
- Efficient Communication:┬ĀDigital literacy improves communication that creates a more efficient workflow. It allows employees to communicate with each other through various platforms, such as email, instant messaging, video conferencing, and social media.
- Enhances Problem-Solving Skills:┬ĀWith digital literacy, employees can access vast amounts of information through the internet, which allows them to research solutions to complex problems, find relevant data, and make informed decisions.
- Increases Efficiency: Digital tools such as automation, online collaboration platforms, and project management software can increase efficiency in the workplace.
- Improves Creativity:┬ĀDigital literacy can also foster creativity in employees by providing access to various digital tools that can unleash their creative potential and produce high-quality content.
- Better Time Management:┬ĀDigital literacy can help employees manage their time more effectively.
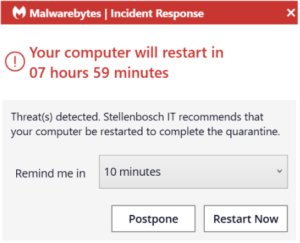
- Online Security:┬ĀDigital literacy skills help individuals understand the importance of securing their online information and the potential risks of cyber-attacks.
- Artificial Intelligence (AI):┬ĀDigital literacy skills are crucial for leveraging AIŌĆÖs benefits.
- Big Data:┬ĀDigital literacy skills have become essential for individuals to interpret and analyse vast amounts of data effectively.
- Social Media:┬ĀDigital literacy skills are essential for using social media safely and responsibly. It enables individuals to identify potential risks associated with social media.
Start your digital literacy pathway
With the Microsoft Digital Literacy classes, you can gain skills needed to effectively explore the internet.┬Ā
Sources:
YOTTABYTE
Microsoft
Futurelab


 Part of living in a connected world is understanding that our private information is more vulnerable. ID theft and data breaches are no longer isolated incidents, they happen every single day.
Part of living in a connected world is understanding that our private information is more vulnerable. ID theft and data breaches are no longer isolated incidents, they happen every single day. The US government’s Cybersecurity and Infrastructure Security Agency has made a collection of tip sheets available for use. These downloadable PDF documents contain all the information you need to protect yourself from cyber security risks in a convenient, compact format.┬Ā
The US government’s Cybersecurity and Infrastructure Security Agency has made a collection of tip sheets available for use. These downloadable PDF documents contain all the information you need to protect yourself from cyber security risks in a convenient, compact format.┬Ā