 Microsoft recently sent out a notification that some versions of Office 2013 and Office 2016 may experience connectivity issues due to the retirement of support for these versions. It is therefore imperative that all users who still use┬Ā Office 2013 and Office 2016 immediately upgrade their Office software to Office 365.┬Ā
Microsoft recently sent out a notification that some versions of Office 2013 and Office 2016 may experience connectivity issues due to the retirement of support for these versions. It is therefore imperative that all users who still use┬Ā Office 2013 and Office 2016 immediately upgrade their Office software to Office 365.┬Ā
Users whose devices are still using Windows XP, Windows 7 and Windows 8 as operating systems are also required to urgently upgrade their devices as this software is no longer supported by Microsoft.
Benefits of upgrading your software
With the challenges we’ve faced over the few months, why do we have to sacrifice valuable time to have my software upgraded?
New malware is released daily, putting your data and the University at risk.┬Ā So, apart from gaining new features by updating your software you are also protected from outsider threats as the new software has better security features, is more reliable and has better performance.┬Ā
When must I do this?
We recommend that users do this upgrade as soon as possible to ensure that you donŌĆÖt fall prey to malware and lose valuable data.
Who will help me with the upgrade?
A support ticket can be logged on the ICT Partner Portal.┬Ā As soon as the ticket is logged, you will receive a reference number via email after which an IT technician will contact you to arrange an appointment to assess if an upgrade is possible on the device.
[Article by Ronel Reynecke]


 Part of living in a connected world is understanding that our private information is more vulnerable. ID theft and data breaches are no longer isolated incidents, they happen every single day.
Part of living in a connected world is understanding that our private information is more vulnerable. ID theft and data breaches are no longer isolated incidents, they happen every single day. As part of the campus ŌĆ£Going GreenŌĆØ project Facilities Management will be placing e-waste bins at selected spots on campus. We encourage staff and students to use these bins for any non-asset e-waste.
As part of the campus ŌĆ£Going GreenŌĆØ project Facilities Management will be placing e-waste bins at selected spots on campus. We encourage staff and students to use these bins for any non-asset e-waste.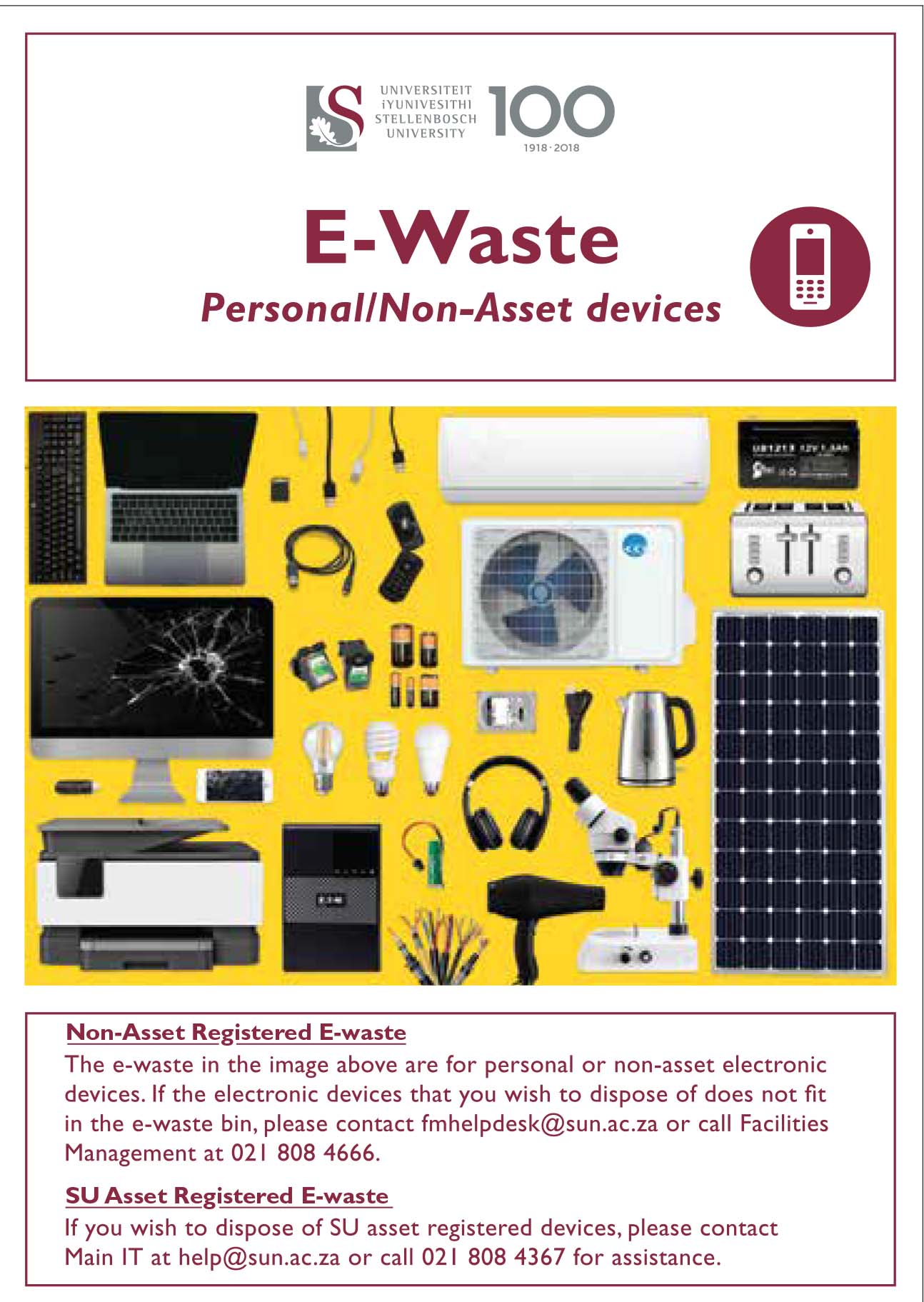
 To ensure that staff and students aren’t exposed to malicious phishing or spam emails our system administrators and security team
To ensure that staff and students aren’t exposed to malicious phishing or spam emails our system administrators and security team