Category: Editorial
5 ways to spot a spear-phishing attack…
by David Wiles | Sep 25, 2019 | CyberSecurity Month, Editorial, Security | 0
Spear-phishing is more subtle than conventional phishing. This scam is always attempted with far...
Read MorePhishers are getting smarter…
by David Wiles | Apr 23, 2019 | Editorial, Security | 0
How many phishing e-mails have you received in the past week? Even with all the filtering and...
Read MoreThe Psychology of Phishing
by David Wiles | Jan 31, 2019 | Editorial, Security | 0
[Inspired by an article in the Kaspersky Lab Blog by Anastasia Gridasova linked here.] If I was to...
Read MoreSpear-phishing is not a new water sport…
by David Wiles | Aug 7, 2017 | Editorial, Reviews & Opinions | 0
According to the South African Banking Risk Information Centre (SABRIC), South Africans lose in...
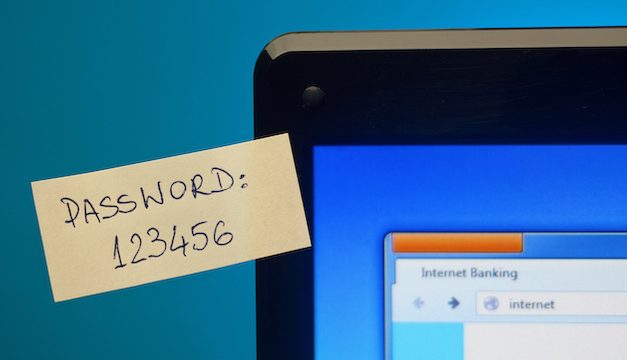
Read MoreHow strong is your password – really?
by David Wiles | Aug 7, 2017 | Editorial, Reviews & Opinions | 0
As if the recent ransomware scares and cleverly disguised phishing scams weren’t enough to...
Read MoreIdentity Theft – Giving out your cellphone number
by David Wiles | Jul 25, 2017 | Editorial, Security, Tips | 0
These days, it seems we have to hand out our cellphone number like sweets at a kids party. Whether...
Read MoreReusing passwords – A bad and dangerous habit
by David Wiles | Jul 24, 2017 | Editorial, Reviews & Opinions | 0
According to International Business Times, a new study finds more than 80% of Americans reuse...
Read MoreTech Support Scams – Bollywood-style
by David Wiles | Jan 15, 2015 | Editorial, Tips | 0
Have you ever received a call from someone with a heavy Indian accent from Microsoft saying your...
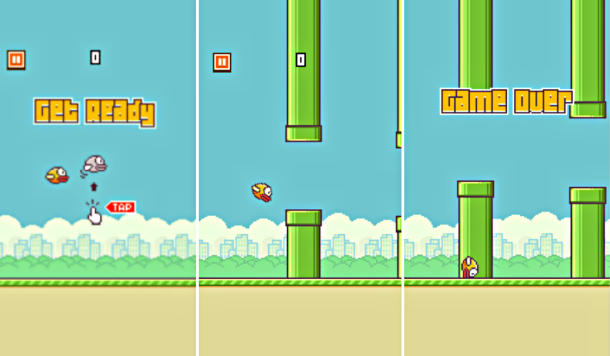
Read MoreScammers are like vultures
by David Wiles | Feb 12, 2014 | Editorial | 0
For those who have been spared the torture of Flappy Bird, it was the latest mobile gaming craze...
Read MoreWW-III: War on WordPress 3
by David Wiles | Apr 14, 2013 | Editorial, Reviews & Opinions | 0
Since 12 April 2013, the WordPress blog system world-wide is facing its most serious coordinated...
Read MoreE-Mail Hoaxes – sometimes as dangerous as the real thing
by David Wiles | Mar 15, 2013 | Editorial, Tips | 0
What is a Virus/E-Mail Hoax? Have you ever received an e-mail message that includes something like...
Read MoreSouth Africa’s spammers
by David Wiles | Nov 23, 2011 | Editorial | 0
ISPA names and shames South Africa’s biggest spammers and email address resellers in their Hall of...
Read More
Recent Posts
Archives
- October 2021
- November 2019
- October 2019
- September 2019
- June 2019
- April 2019
- March 2019
- February 2019
- January 2019
- November 2018
- October 2018
- August 2018
- November 2017
- August 2017
- July 2017
- June 2017
- May 2017
- December 2016
- January 2015
- February 2014
- August 2013
- July 2013
- June 2013
- April 2013
- March 2013
- May 2012
- March 2012
- November 2011
- October 2011
- June 2011
- May 2011
- April 2011
- December 2010
- October 2010
- May 2010
- April 2010
- November 2009
- October 2009
- September 2009
- August 2009
- July 2009
- June 2009
- May 2009
- April 2009
- March 2009